Mastering Springboot Security

Introduction to security with Basic Auth


Learning Outcome
5
Learn authentication process using providers and services
4
Understand role of DelegatingFilterProxy in security
3
Analyze request flow through security filter chain
2
Differentiate authentication and authorization concepts clearly
1
Understand Spring Security fundamentals and architecture

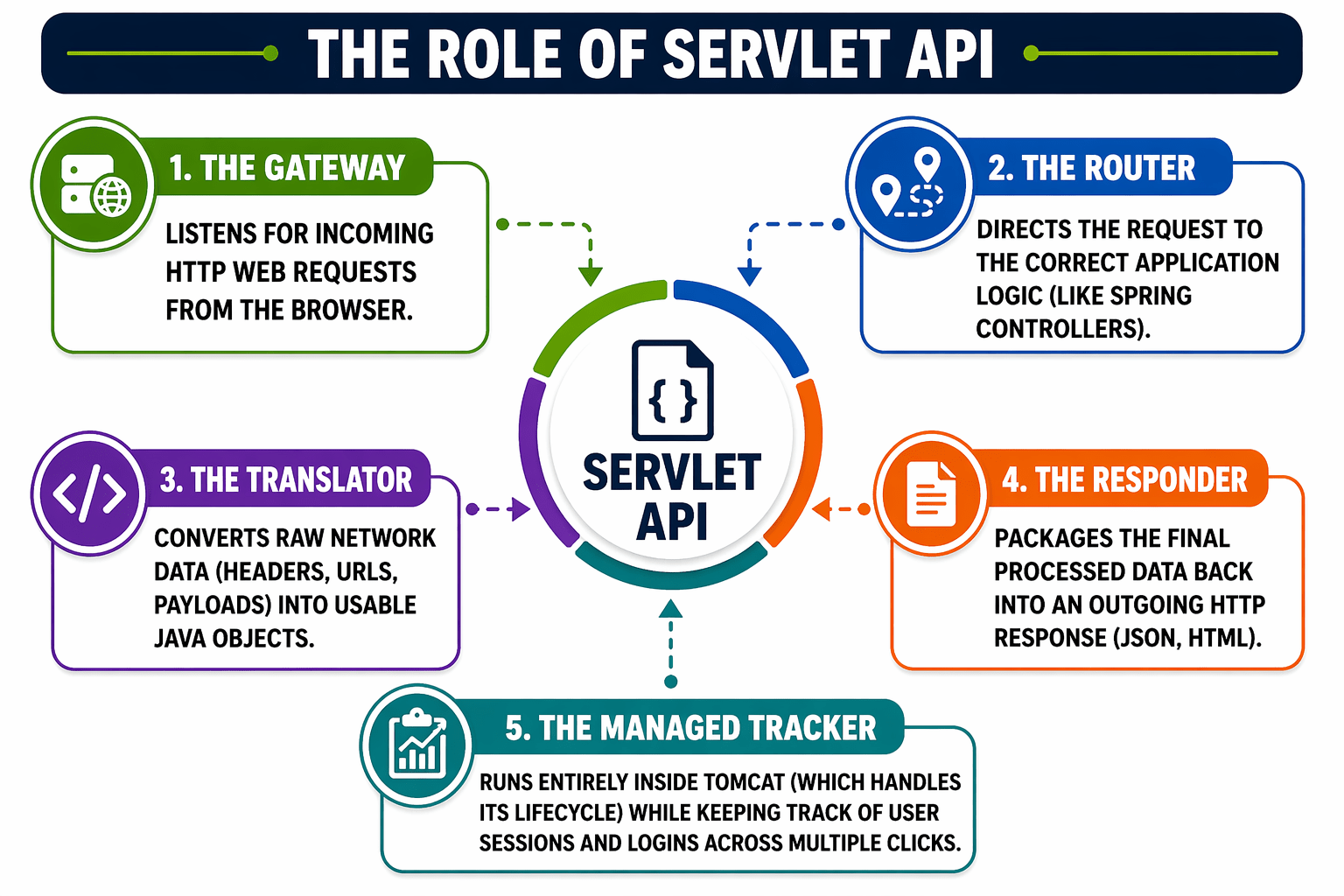
Spring Security is the standard framework for securing Spring-based applications. It works alongside Spring Boot to protect applications from unauthorized access and security threats.
Introduction to Spring Security

It is the de facto standard framework for securing Spring applications and ensures protection against unauthorized access and malicious attacks.
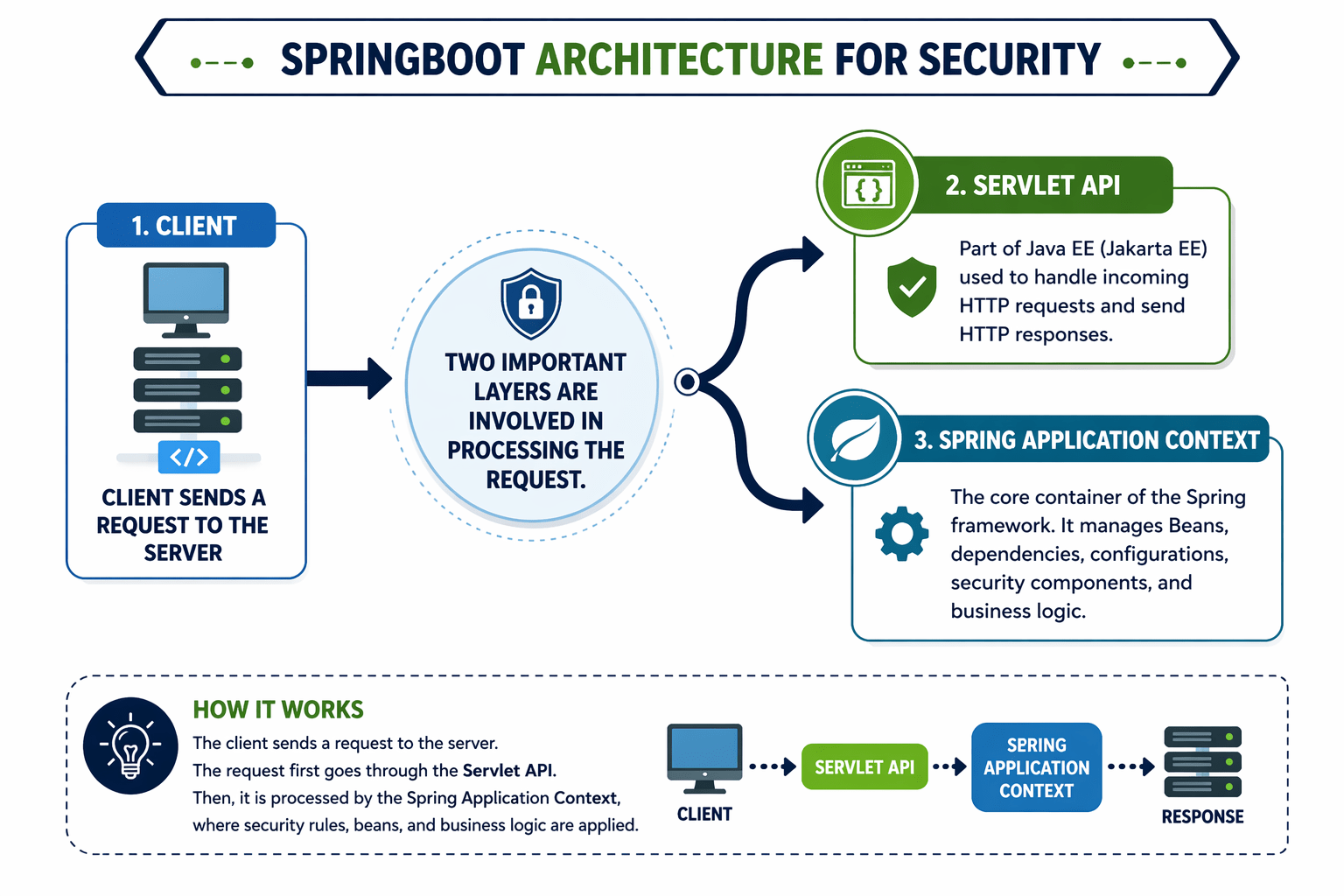
It functions internally by utilizing a sophisticated chain of customized Servlet Filters.
These filters intercept HTTP requests before reaching controllers, allowing validation of credentials and permissions at the application’s edge.

Spring Security is the standard framework for securing Spring-based applications. It works alongside Spring Boot to protect applications from unauthorized access and security threats.
Introduction to Spring Security

It is the de facto standard framework for securing Spring applications and ensures protection against unauthorized access and malicious attacks.
It functions internally by utilizing a sophisticated chain of customized Servlet Filters.
These filters intercept HTTP requests before reaching controllers, allowing validation of credentials and permissions at the application’s edge.

Security in any application boils down to two distinct but deeply connected concepts...


Authentication
Authorization
- Authentication verifies the identity of the user.
- It ensures the user is who they claim to be.
- Authorization determines what the user can access.
- It ensures the user has the right permissions.

How Authentication works ?

User
Requests
Submit
Credentials

Verify
Credentials

Authentication
Successfull

If the authentication fails, the application returns a 401 Unauthorized status.

How Authorization works ?


Verify
Credentials
Authenticated
User

Access
Resources


Access
Granted
If you are logged in but try to access an area you shouldn't, the application returns a 403 Forbidden status.

Features of Spring Security
1. Secure Endpoints Automatically
Spring Security's "Secure by Default" feature auto-configures security when you add the spring-boot-starter-security dependency, locking all API endpoints and requiring authentication without any code.
2. Supports Multiple Authentication Methods
- Form Login: User enters credentials via webpage
- HTTP Basic: Credentials sent in request headers.
- JWT / OAuth2: Stateless token-based auth, supports third-party login

3. Built-in Protection Against Common Exploits
- CSRF: It is an attack that tricks a logged-in user into performing unwanted actions, and Spring Security prevents it by validating requests using CSRF tokens.
- Session Fixation: It is an attack where a user is forced to use a known session ID, and Spring Security prevents it by creating a new session ID after login.
4. Highly Customizable
Spring Security is secure by default yet highly flexible, allowing developers to customize behavior using SecurityFilterChain for features like custom user fetching, role management, and IP filtering.

Springboot Architecture for Security

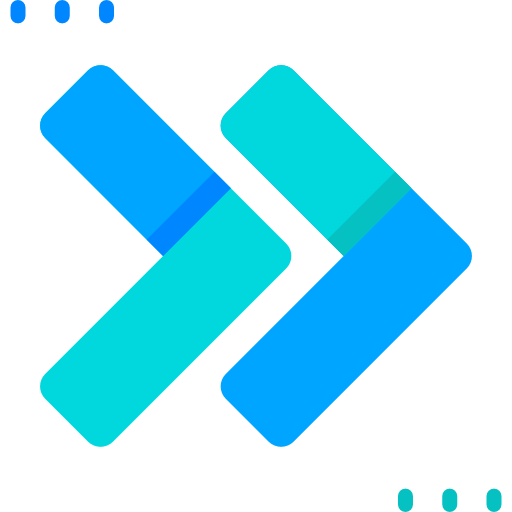
Client sends a request to the server




Coming back to Request flow
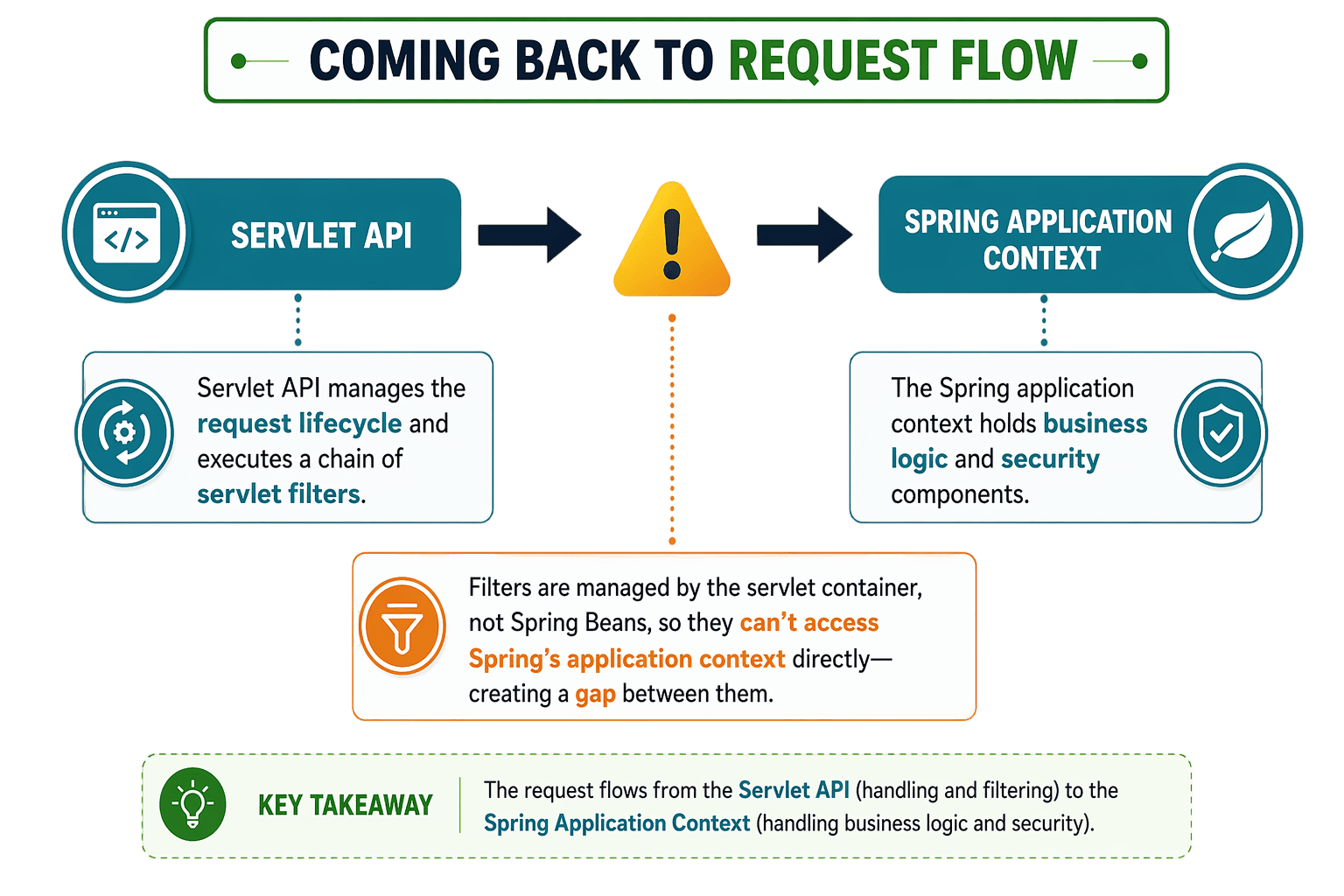

Coming back to Request flow
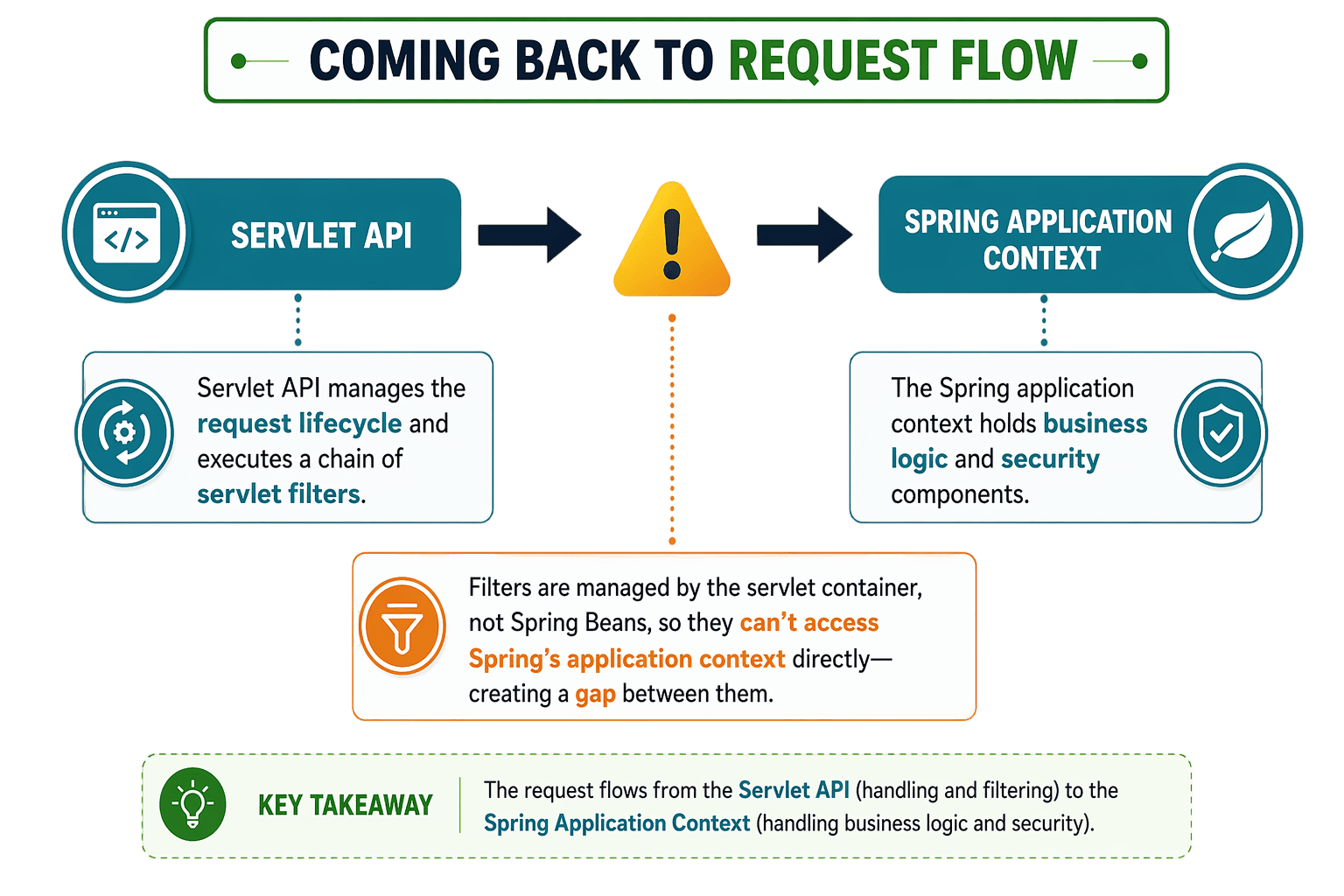

Coming back to Request flow
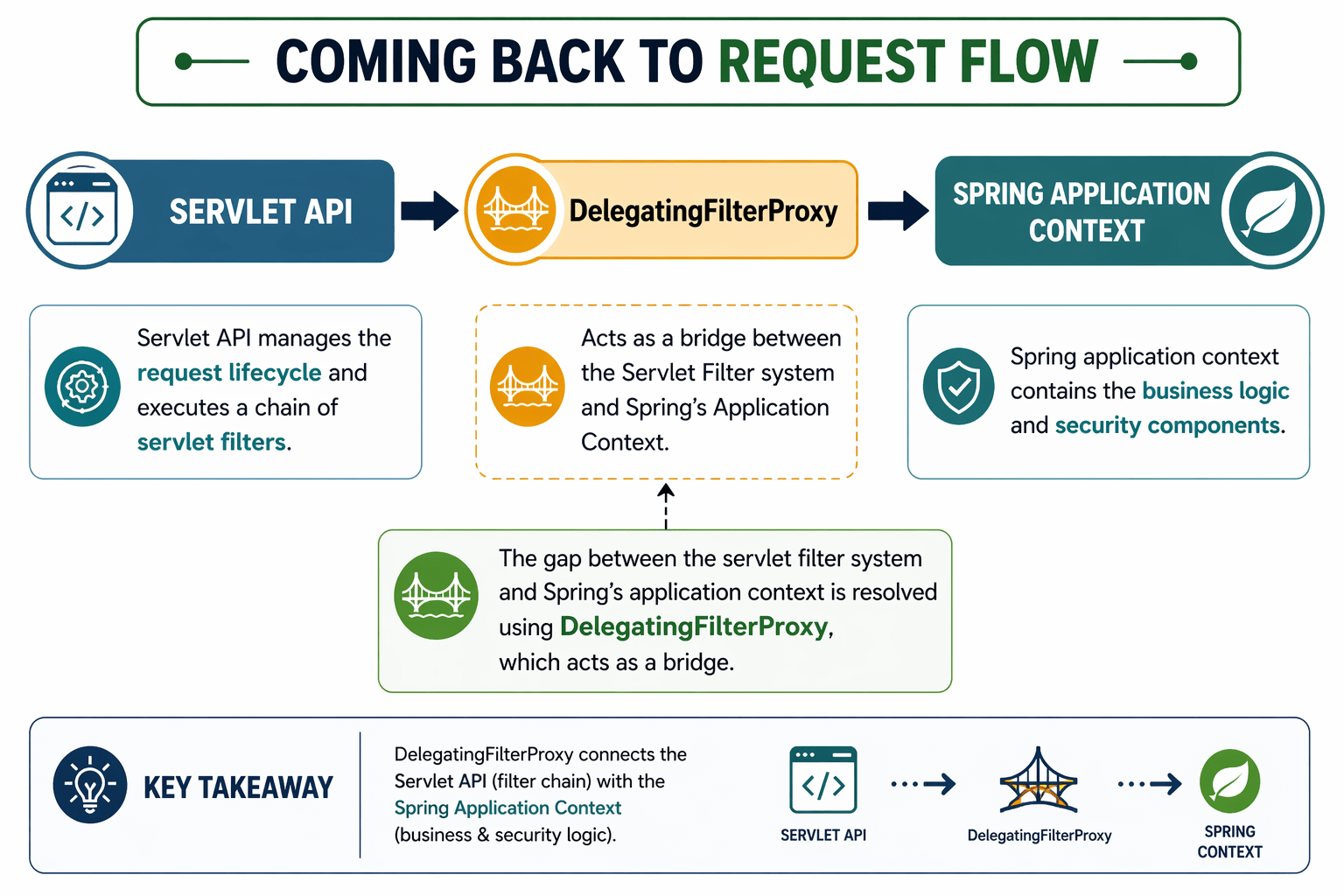
Note: DelegatingFilterProxy does not contain the security logic itself.


Flow of Request
DelegatingFilterProxy
It just Delegates request to springSecurityFilterChain
(FilterChainProxy)
FilterChainProxy
Filters
Filters
Filters
Filters
ServletFilterChain

Flow of Request
DelegatingFilterProxy
FilterChainProxy
Filters
Filters
Filters
Filters
ServletFilterChain
SecurityFilterChain 1
Filters
Filters
SecurityFilterChain 2
Filters
Filters
SecurityFilterChain 3
Filters
Filters
FilterChainProxy
manages multiple SecurityFilterChains and selects the appropriate one based on request rules (e.g., URL patterns).

Flow of Request
SecurityFilterChain 1
Filters
Filters

Once the appropriate SecurityFilterChain is selected,

Role of SecurityFilterChain
SecurityFilterChain 1
Filters
Filters

Once the appropriate SecurityFilterChain is selected,
it executes a list of filters responsible for authentication and authorization.
UsernamePasswordAuthenticationFilter
BasicAuthenticationFilter
custom filters such as JWTAuthFilter
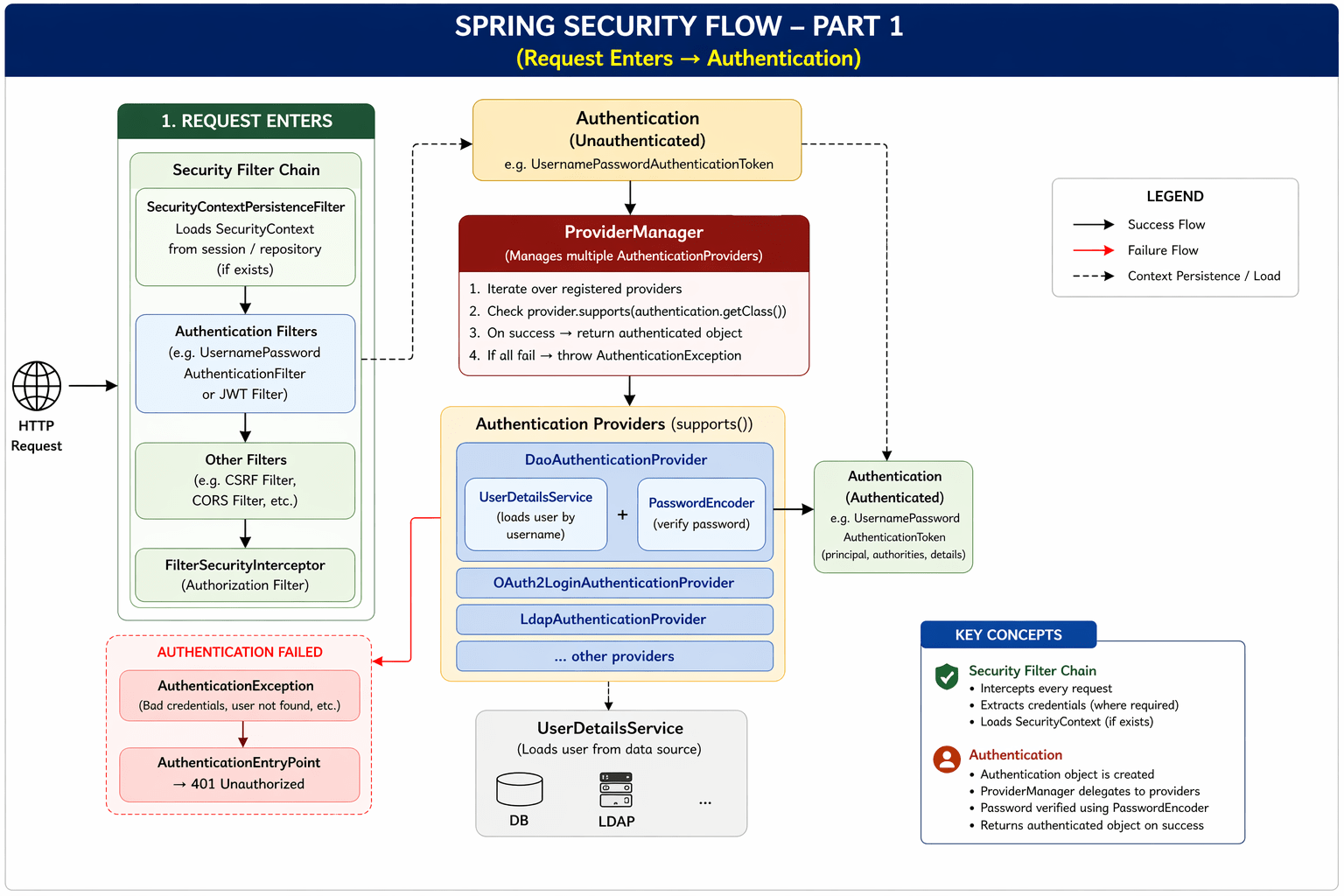
Authentication begins when a filter detects an authentication request

Flow of Request
SecurityFilterChain 1
Filters
Filters
UsernamePasswordAuthenticationFilter
For example :-
it extracts the username and password from the request, creates an Authentication object,

Flow of Request
SecurityFilterChain 1
Filters
Filters
UsernamePasswordAuthenticationFilter
For example :-
that Authentication object is delegated to the AuthenticationManager.
Authentication Manager(interface)
ProviderManager
(implementation)

Flow of Request
SecurityFilterChain 1
Filters
Filters
UsernamePasswordAuthenticationFilter
that Authentication object is delegated to the AuthenticationManager.
Authentication Manager(interface)
ProviderManager
(implementation)
The AuthenticationManager is an interface that defines the contract for authentication. Its default implementation is ProviderManager, which handles the actual authentication process.

Flow of Request
SecurityFilterChain 1
Filters
Filters
UsernamePasswordAuthenticationFilter
Authentication Manager(interface)
ProviderManager
(implementation)
Authentication Providers
supports()
DaoAuthenticationProvider
OAuth2LoginAuthenticationProvider
LdapAuthenticationProvider
ProviderManager sends and Iterates through AuthenticationProviders
Uses supports() to find the right provider
Only the matching provider performs authentication
Validates credentials via authenticate() and returns result

Flow of Request
Authentication Providers
supports()
DaoAuthenticationProvider
OAuth2LoginAuthenticationProvider
LdapAuthenticationProvider
But Once the AuthenticationProvider receives the Authentication request, a key question arises
how does it validate the username and password?

Flow of Request
Authentication Providers
supports()
DaoAuthenticationProvider
OAuth2LoginAuthenticationProvider
LdapAuthenticationProvider
UserDetailsService
which is an interface responsible for retrieving user information
The AuthenticationProvider delegates the task of loading user data to this service.
InMemoryUserDetailsManager
JdbcUserDetailsManager

Flow of Request
Authentication Providers
supports()
DaoAuthenticationProvider
OAuth2LoginAuthenticationProvider
LdapAuthenticationProvider
UserDetailsService
which is an interface responsible for retrieving user information
The AuthenticationProvider delegates the task of loading user data to this service.
InMemoryUserDetailsManager
JdbcUserDetailsManager
Depending on your setup, implementations like InMemoryUserDetailsManager or JdbcUserDetailsManager can be used to fetch user details either from memory or a database.


Flow of Request
However, passwords in a database are not stored in plain text—they are stored in an encoded (hashed) format for security reasons
When a user submits a login request, the raw password must be compared with the encoded password from the database. This is handled using a PasswordEncoder.

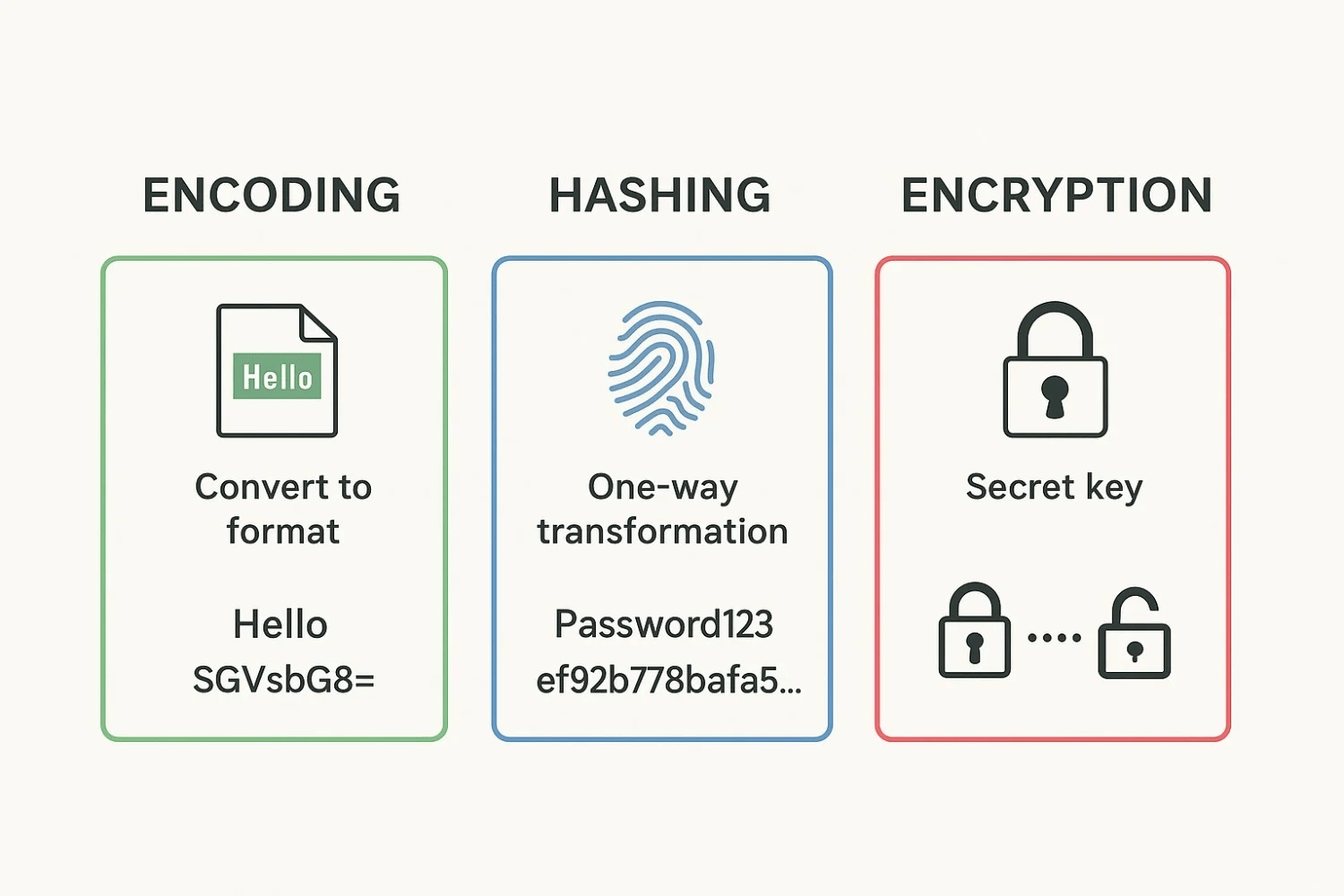
The PasswordEncoder encodes the incoming raw password and compares it with the stored encoded password. If they match, authentication is successful; otherwise, it fails.

Flow of Request
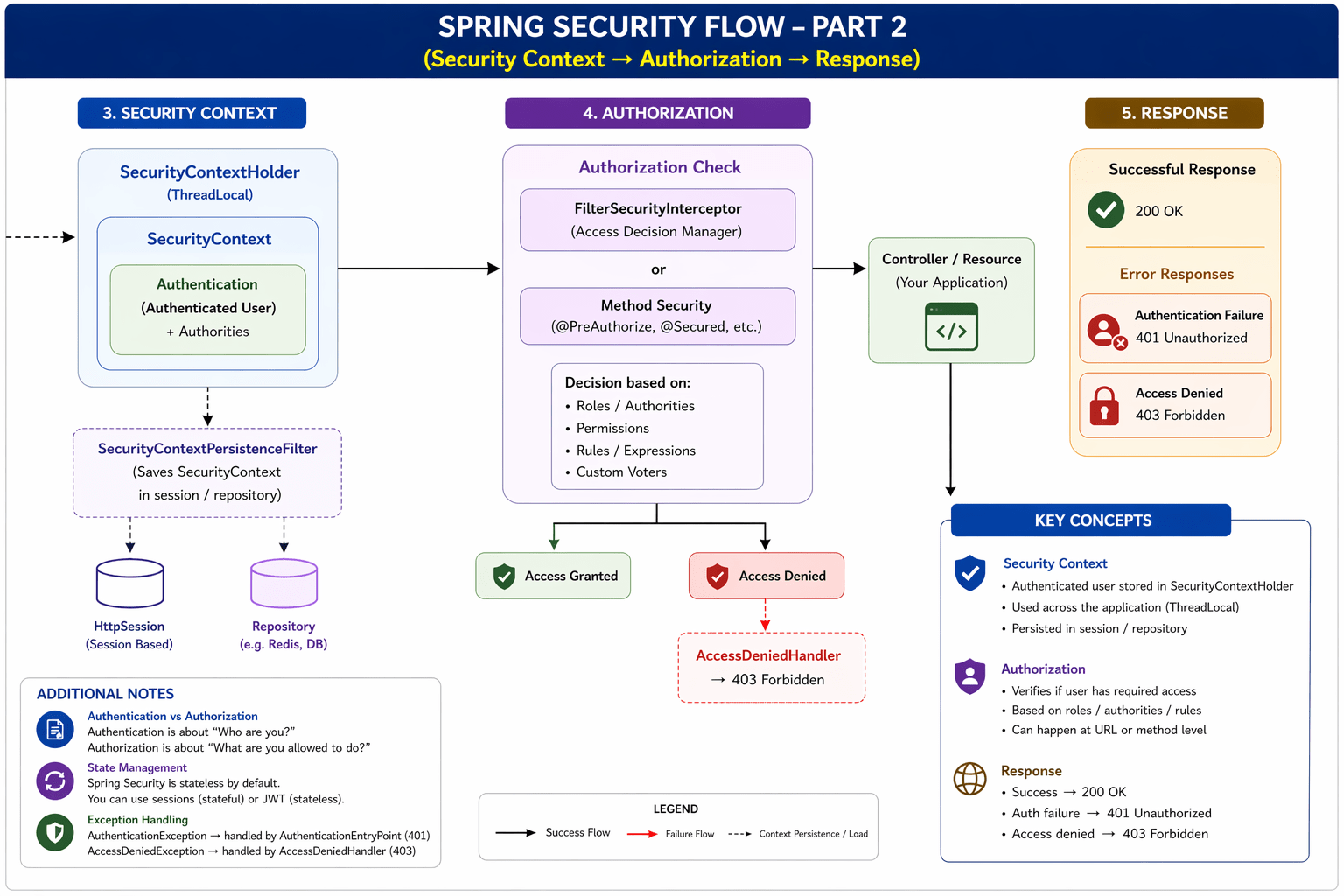
The AuthenticationManager then returns this Authentication object back to the filter that initiated the authentication process. However, this information needs to be stored so that it can be accessed throughout the application during the lifecycle of the request.
To handle this, Spring Security uses a SecurityContext, which stores the Authentication object. This allows other parts of the application to access the details of the currently authenticated user.

Flow of Request
The securitycontext stores the authenctionation object which is also called has principle object and in order to access that inside your springboot appliaction
Spring has provided kind of an abstraction which is securitycontextholder
Access to the SecurityContext is provided through the SecurityContextHolder, which offers methods like getContext() to retrieve the current Authentication (or principal) object. This enables any component in the application to check who the user is and what permissions they have.



Summary
5
UserDetailsService retrieves user data for validation
4
Authentication handled using AuthenticationManager and providers
3
DelegatingFilterProxy bridges servlet and Spring context
2
Filters intercept requests before reaching controllers
1
Spring Security protects applications from unauthorized access

Quiz
Which component acts as a bridge between the Servlet Filter chain and Spring Application Context?
A. AuthenticationManager
B. FilterChainProxy
C. DelegatingFilterProxy
D. UserDetailsService

Which component acts as a bridge between the Servlet Filter chain and Spring Application Context?
A. AuthenticationManager
B. FilterChainProxy
C. DelegatingFilterProxy
D. UserDetailsService
Quiz-Answer
