Book 2. Credit Risk
FRM Part 2
CR 2. Governance

Presented by: Sudhanshu
Module 1. Governance and Risk Management
Module 2. Credit Risk Guidelines
Module 1. Governance and Risk Management

Topic 1. Effective Governance and Risk Taking Processes
Topic 2. Three Lines of Defense Framework

Topic 1. Effective Governance and Risk Taking Processes
-
Effective governance provides a framework for achieving an organization's objectives.
-
A key component is superior risk management, where risk managers help balance business needs with protecting the organization from undue risks.
-
The CEO is ultimately responsible for ensuring that adequate governance guidelines have been established and should have the support of their staff.
-
The main processes that are involved in risk-taking are:
-
Credit Origination: The process of acquiring or creating a credit-sensitive asset. This is typically driven by business units or originators who identify potential transactions.
-
Credit Risk Assessment: The evaluation of a proposed transaction to identify, measure, and price the risk. This step is a collaboration between the originator and the risk manager.
-
Credit Approval: The formal process of obtaining approval for the transaction. This involves an internal approval committee or an individual with delegated authority, based on the transaction's risk.
-
-
Three Lines of Defense (LoD) Framework:
-
First Line: Business owners who own and manage risks directly.
-
Second Line: ERM, compliance, and legal functions that monitor and oversee risks.
-
The second line establish policies and procedures.
-
The second line oversees the first line.
-
-
Third Line: Internal and external auditors, and audit committees who provide independent risk monitoring and assessment.
-
Topic 2. Three Lines of Defense Framework
Practice Questions: Q1
Q1. To ensure an adequate second line of defense, organizations should:
A. include the compliance and legal functions in risk oversight.
B. look primarily to business owners because they own and manage the risks.
C. ensure that the first line of defense has proper oversight of the second line.
D. ensure that the audit function provides an independent risk management role.
Practice Questions: Q1 Answer
Explanation: A is correct.
Effective risk management and control is based on three lines of defense: first line (business owners), second line (enterprise risk management, compliance, and legal functions), and third line (internal and external auditors and audit committees). The second line provides oversight of the first line.
Module 2. Credit Risk Guidelines

Topic 1. Key Principles of Governance
Topic 2. Guidelines (Credit Policies)
Topic 3. Creation and Approval
Topic 4. Maintenance and Control
Topic 5. Breach and Noncompliance
Topic 6. Skills
Topic 7. Limits
Topic 8. Oversight
Topic 9. Transaction Parameters
Topic 10. Credit Committee









Topic 1. Key Principles of Governance
-
Effective governance is based on the following four key principles:
-
Guidelines: Organizations must institute clear guidelines around approvals, including approvals for transactions that give rise to credit risk.
-
Skills: Authority must be delegated to those with proper skills.
-
Limits: Adequate risk and transaction limits must be set.
-
Oversight: Employees and functions should be subject to oversight by qualified and independent people.
-
Topic 2. Guidelines (Credit Policies)
-
Define the rules for how transactions are conducted and should be understandable, concise, precise, and accessible. The language should be clear and straightforward, avoiding legal jargon.
-
Content: Guidelines should cover the purpose, methodology, transaction approval flow, how to handle new products and markets, the review process, and consequences for employees who breach or fail to adequately follow them.
-
Creation & Approval:
-
Guidelines are sponsored by the CFO or CRO and approved by the Board of Directors and its risk committees.
-
They should be reviewed periodically for content and accuracy, especially after changing regulations, major events like mergers and acquisitions or significant losses.
-
Maintenance: The CRO's office is responsible for drafting, approving, and maintaining the guidelines. Those drafting the guidelines should have sufficient seniority and expertise to deal professionally with potential conflicts with business units.
-
Topic 3. Creation and Approval
-
Risk protection role: Guidelines are designed to protect the organization against risk and must include appropriate authorizations.
-
Management accountability: Senior management is ultimately responsible for the guidelines and their effectiveness.
-
Executive sponsorship: Best practice is for guidelines to be sponsored by the CFO or CRO.
-
Board oversight: Guidelines should be approved by the board of directors, typically through a risk committee.
-
Ongoing review: Guidelines must be reviewed periodically to ensure accuracy and alignment with current practices and regulations.
-
Quality checks and triggers: The board and risk committees may request updates, and any loss event should trigger a review of relevant guidelines.
-
Forward-looking risk consideration: Risk managers should assess low-probability but high-impact scenarios, such as negative interest rates or negative commodity prices.
Topic 4. Maintenance and Control
-
CRO ownership: The Chief Risk Officer (CRO) typically owns the risk guidelines, with the CRO’s office responsible for drafting, approving, and maintaining them.
-
Expert authorship: Guidelines should be drafted by individuals with sufficient seniority, expertise, and understanding of the firm’s products and markets.
-
Conflict management: Because guidelines can create tension between risk managers and business units, conflicts must be handled professionally, ideally by senior management.
-
Periodic review: Guidelines should be reviewed regularly to reflect the evolving regulatory environment, which has become more stringent since 2008.
-
Event-driven updates: Significant organizational events, such as mergers and acquisitions, may require substantial modifications to existing guidelines.
-
Guideline topics should include:
-
the purpose of the guidelines
-
the methodology used
-
transaction approval flow and delegation of authority
-
the process on handling new products and markets
-
the process to review/update the guidelines
-
consequences for employees who breach or fail to adequately follow guidelines
-
Topic 5. Breach and Noncompliance
-
Rarity of breaches: Breaches of established risk guidelines are expected to be infrequent.
-
Severe consequences: Serious or intentional breaches can result in disciplinary action, including termination of employment.
-
Tolerance for natural breaches: Some unintentional breaches (e.g., due to FX rate movements affecting credit limits) may be tolerated through predefined carve-outs.
-
Centralized exposure tracking: Firms maintain centralized databases of transaction exposures and credit parameters.
-
Pre-trade controls: Pre-trade checks allow originators to verify transaction permissibility, automatically preventing or flagging unauthorized trades.
Practice Questions: Q1
Q1. A firm’s risk management unit is updating their guidelines relating to transaction approval and delegation. Risk managers are worried that even when transactions fall within available credit limits, foreign exchange volatility may cause breaches in these limits. Which of the following guideline parameters would be most appropriate to deal with this type of outcome?
A. The guidelines should include a carve-out for breaches that are due to foreign exchange rate volatility.
B. Breaches in the credit limit due to foreign exchange rate movements should be immediately escalated to the chief risk officer (CRO).
C. The guidelines should treat each breach in the credit limit as an error by the originator, because currency movements should be anticipated.
D. Breaches in the credit limit due to foreign exchange rate movements should be immediately escalated to the risk commiee of the board of directors.
Practice Questions: Q1 Answer
Explanation: A is correct.
The firm should include a carve-out in the guidelines to allow for breaches of credit limits due to external factors not within the control of the firm. It is not prudent to treat these breaches as an originator error, and it is not necessary to escalate them if the guidelines include the carve-outs.
Topic 6. Skills: Approval and Delegation of Authority
-
Authority must be delegated to professionals with the proper skills and experience.
-
Approval:
-
Delegated risk authority: Since senior management and boards cannot approve every transaction, risk authority is delegated to experienced risk professionals across the organization.
-
Business partnership mindset: Risk managers must understand the business and build strong relationships with originators, as the risk function is often seen as a constraint on growth.
-
Advisory-not profit-role: Risk management is not a profit center and typically does not have direct approval authority; it serves an advisory role to the business.
-
Clear governance guidelines: Policies should clearly define when and how risk manager input is required in decision-making.
-
Escalation and dissent: Although risk managers usually lack veto power, they can formally express dissent through written memos escalated to credit or risk committees.
-
-
Delegation of Authority: The process has two key steps:
-
Step 1: Assigning risk parameters to each transaction (amount of exposure, credit quality, tenor), and
-
Step 2: Delegating authority based on those parameters.
-
Topic 6. Skills: Approval and Delegation of Authority
-
Risk-based approvals: Approval authority should scale with transaction risk, with simple, low-risk transactions approved at lower levels, often by a single individual.
-
Senior management involvement: Higher-risk, longer-tenor, or lower-credit-quality transactions typically require approval from senior management.
-
Escalation framework: The approval process is commonly structured as a risk–approval flow, clearly outlining how delegation escalates as transaction risk increases.
-
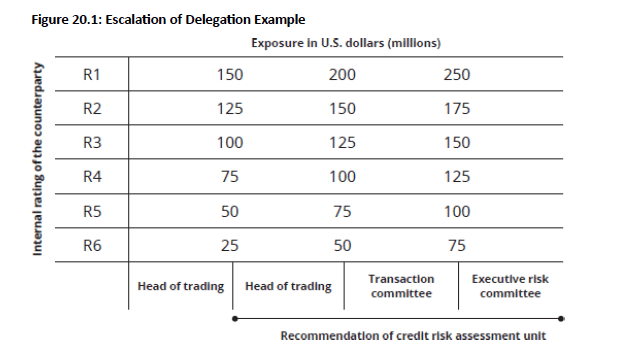
Example: From below table, a transaction with an exposure of $110 million with a counterparty rated R4 would require approval by the transaction committee (which has approval for an R4 counterparty up to $125 million). The transaction also requires the recommendation of the credit risk assessment unit (which reviews transactions exceeding $75million).
Topic 7. Limits
-
Definition of limits: Risk limits (credit lines) specify the maximum absolute dollar loss an organization is willing to accept.
-
Hierarchical allocation: An overall firm-wide limit (e.g., $75 million) is typically broken down into smaller limits by counterparty, sector, industry, or country.
-
Broad applicability: Absolute limits work well for most transactions but can be difficult to estimate for dynamic, long-term exposures such as physical commodity trades or derivatives.
-
Risk assessment basis: Limit setting combines quantitative exposure analysis with management judgment on acceptable risk levels.
-
Role of intuition: Management intuition, shaped by experience and risk appetite, plays a key role in determining limits.
-
External influence: Limits are influenced by what regulators, rating agencies, and shareholders consider acceptable.
-
Business-level limits: Beyond firm-wide caps, limits are assigned to individual businesses, with originators often preferring preapproved limits to streamline client marketing and deal execution.
Topic 8. Oversight
-
Effective oversight requires independence, strong qualifications, closeness to the business, and an open mind.
-
Independence: Risk management should not be located within a profit center.
-
To ensure independence, risk managers should report to the CRO instead of business unit heads. The CRO typically reports directly to the CEO and has direct access to the Board's risk and audit committees.
-
-
Strong qualifications: Risk managers must understand business models, incentives, and transaction structures, and may attend client meetings to articulate risk positions.
-
They should enter such discussions with clear, limit-based positions and avoid emotional or client-driven pressure.
-
-
Closeness to the business: Risk managers must avoid becoming too close to business units so they can remain an objective and independent voice on risk.
-
Open Mind: A good risk manager balances business needs with protecting the organization's interests.
-
While independent, they should still be familiar with the business units, profit drivers, and transaction structures.
-
Practice Questions: Q2
Q2. Which of the following statements about risk managers’ reporting structure is most accurate?
A. To be most effective, risk managers should report to the business unit heads.
B. To preserve their independence, risk managers should report directly to the CRO.
C. Risk managers should have dotted line reporting to both the CRO and business unit heads.
D. To ensure effective risk governance, risk managers should report directly to the board of directors.
Practice Questions: Q2 Answer
Explanation: B is correct.
Risk managers should report to the CRO instead of the business unit heads to ensure they remain independent and free of business influence. CROs have influence at the top organization level including the CEO and risk committees. It would not be feasible for risk managers to report directly to the Board, which deal with broad oversight of risks rather than more granular risk matters.
Topic 9. Transaction Parameters
-
Credit-sensitive transactions are defined by three key parameters:
-
Amount of Exposure: The amount of potential losses in the transactions.
-
Credit Quality: The assessment of the creditworthiness of counterparties to understand the risk of losses.
-
Length of Exposure (Tenor): The period of time an organization is exposed to potential losses.
-
Practice Questions: Q3
Q3. A firm recently developed a model to help summarize the creditworthiness of each of its counterparties. Which of the following risk parameters of a credit-sensitive transaction does this most likely represent?
A. Tenor.
B. Credit quality.
C. Maximum loss.
D. Amount of exposure.
Practice Questions: Q3 Answer
Explanation: B is correct.
Parameters of credit-sensitive transactions include credit quality (assessing the creditworthiness of counterparties and the risk of losses due to counterparty exposure), the amount of exposure (measuring losses), and length of exposure (period during which risk exposure exists).
Topic 10. Credit Committee
-
Role and composition: The credit committee typically consists of senior executives and is responsible for approving significant or high-risk transactions.
-
Clear governance: The committee operates under a formal charter that clearly defines approval authority, roles, and decision-making processes.
-
Preparation and review: Transactions are presented as detailed packages by originators well in advance, allowing sufficient time for thorough review.
-
Decision discipline: An effective committee demonstrates balanced judgment, with a track record of both approvals and declines.
-
Cross-functional expertise: Membership includes representatives from key functions such as business units, risk management, tax and accounting, compliance, and legal, with strong risk expertise.
-
Accountability and leadership: Members are decision-makers with limited delegation, led by an objective chair who facilitates discussion and calls for a vote if consensus is not reached.
-
Documentation: Meeting minutes are formally recorded and distributed promptly after each committee meeting.
Copy of CR 2. Governance
By Prateek Yadav
Copy of CR 2. Governance
- 140



